We scanned 50,000 repos once. By the time you read this, the results are already stale. Developers have added new workflows, changed action versions, and introduced new injection sinks. A scan captures a moment. Continuous monitoring captures the trajectory.
The Setup
This entire research series - from the pillar findings through the supply chain crisis, the chain attack anatomy, and the AI force multiplier - is based on a single scan. 50,012 repos. One point in time. March 2026.
The findings are real. The data is accurate. And it’s already aging.
In the time between our scan and your reading of this article, repositories have added new workflow files, updated action versions, changed permission blocks, added new triggers, and introduced new expression interpolation patterns. Some of the 20,265 vulnerable repos have been fixed. Some of the 29,747 clean repos have introduced new vulnerabilities. The dataset is a snapshot - useful for understanding the scope of the problem, insufficient for maintaining security.
This is the fundamental limitation of point-in-time scanning, and it’s the problem this article addresses.
The Snapshot Blindness Problem
Snapshot Blindness is the gap between what a single scan reveals and what’s actually happening in a continuously evolving environment. Every security tool that runs once and reports results suffers from it. The report is accurate at the moment of capture and progressively less accurate with every passing day.
In CI/CD, Snapshot Blindness is particularly acute because:
Pipelines change constantly. Developers modify workflows weekly - new build steps, new actions, new deployment targets, new triggers. Each change can introduce or resolve vulnerabilities. A repo that was clean yesterday can have five new findings today because a developer added an unpinned action in a new release workflow.
Action maintainers push updates behind mutable tags. Your pinned-yesterday action could be compromised today. The mutable tag still says @v3, but @v3 now points to different code. Without continuous monitoring, you won’t know until the next manual scan - if there is one.
GitHub releases new features that change the security model. Artifact attestation, OIDC improvements, reusable workflow enhancements, new trigger types - the platform evolves, and each evolution can change the risk profile of existing workflows.
Dependencies shift. The action you depend on changed maintainers. A single-maintainer project went dormant. An organization’s security posture degraded. These are temporal signals that a single scan can’t capture.
The 50K scan we ran is the most comprehensive CI/CD security dataset ever published. And it’s a single frame from a continuous movie. The story it tells is directionally correct but temporally limited.
From Runner Guard to ThreatCert
Vigilant built Runner Guard as the open-source answer to “scan your repos right now.” It’s free, it’s fast, and it detects 14 vulnerability classes that no other scanner covers - including AI config injection (RGS-010, RGS-011) and taint-to-execution chain analysis.
Runner Guard is the right tool for a point-in-time assessment. For continuous monitoring, ThreatCert picks up where Runner Guard leaves off.
What Runner Guard Does
- Scans GitHub Actions workflow files for 14 security rule categories
- Autofix engine for SHA pinning (RGS-007)
- Console, JSON, and SARIF output formats
- Runs locally, in CI, or against remote GitHub repos
- Free and open-source - the tool that powered this 50K-repo research
What ThreatCert Adds
Runner Guard’s scanning engine is integrated into ThreatCert as one of seven intelligence domains. CI/CD Pipeline Intelligence runs continuously alongside:
- Network Intelligence - infrastructure exposure, port scanning, service enumeration
- DNS Intelligence - domain health, dangling records, takeover risks
- TLS/Certificate Intelligence - certificate expiry, weak configurations, chain issues
- Web Application Intelligence - surface-level web security signals
- Dark Web Intelligence - credential leaks, data exposure, threat actor mentions (Coming Q2 2026)
- Social Media Intelligence - brand impersonation, phishing campaigns, reputation signals (Coming Q2 2026)
- CI/CD Pipeline Intelligence - Runner Guard’s engine, running continuously
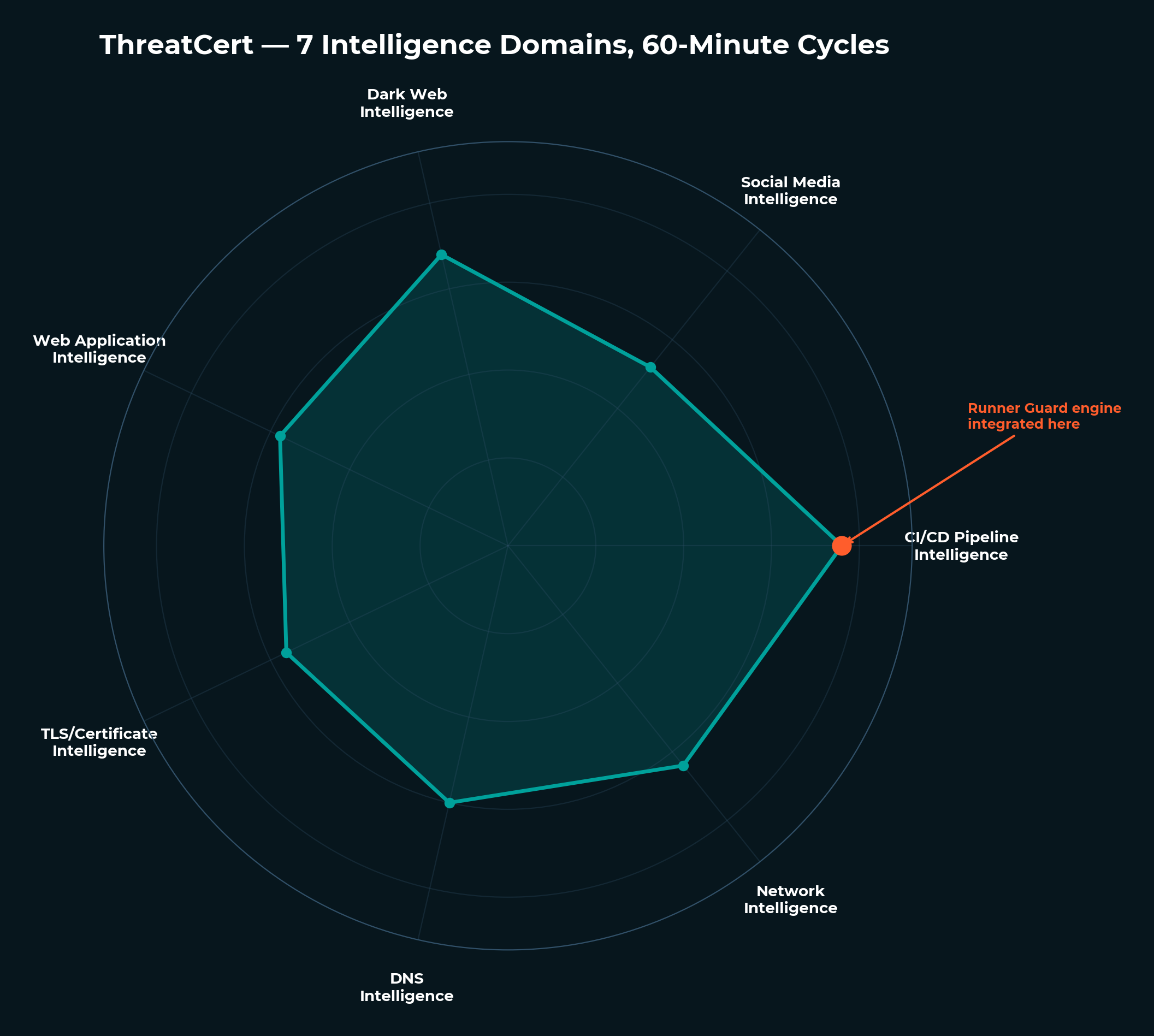
Every 60 minutes, ThreatCert re-evaluates your entire entity landscape - including your CI/CD pipelines and the CI/CD pipelines of your dependencies. When a developer adds an unpinned action or introduces an injection sink, ThreatCert detects it in the next scan cycle - not at the next annual audit, not at the next quarterly review, not when the next incident forces a retroactive investigation.
Temporal Shift Analysis
Single scans show you what’s there now. Temporal Shift Analysis shows you how things are changing - and how fast.
ThreatCert tracks entity attributes over time, detecting when characteristics migrate. A repository that changed maintainers three times in 30 days is fundamentally different from one that’s been stable for two years - even if both have the same vulnerability count right now. A GitHub Action that changed its tag-to-commit mapping twice in a week is a different risk from one that updates quarterly.
Temporal Shift Velocity - the speed of change - becomes its own risk signal. Rapid changes in pipeline configuration, dependency updates, or permission modifications can indicate:
- A legitimate major refactoring (expected, but worth monitoring)
- A compromised account making rapid modifications (the AI-paced attack from our force multiplier analysis)
- A maintainer adding infrastructure for a new deployment target (new attack surface)
- An organization changing CI/CD tooling (dependency landscape shift)
Temporal Shift Analysis catches all of these because it measures velocity, not just state. A snapshot tool sees “this repo has 5 findings.” ThreatCert sees “this repo had 0 findings last week, 2 three days ago, and 5 today - the pipeline is degrading rapidly.”
Attack Condition Alignment Detection
Individual findings are concerning. Aligned conditions across multiple domains are critical.
A single unpinned action is a medium-severity finding. An unpinned action in a repo where:
- The maintainer’s credentials appeared in a dark web dump last month
- The repo’s GITHUB_TOKEN has write permissions
- The workflow processes untrusted input from pull requests
- The CI environment has access to production cloud credentials
…is not a medium-severity finding. It’s an imminent supply chain compromise waiting for an attacker to connect the dots.
ThreatCert’s Attack Condition Alignment Detection correlates CI/CD findings with signals from all seven intelligence domains. The correlation is what transforms individual findings into predictive risk assessment. Runner Guard can tell you the CI/CD pipeline is vulnerable. ThreatCert can tell you that the conditions for exploitation are aligning.
The Organizational Attacker Intent Score
Traditional security metrics count vulnerabilities. ThreatCert’s Organizational Attacker Intent Score (OAIS) asks a different question: how likely is it that an adversary would actually target your organization?
The OAIS considers:
- Entity landscape: What your organization looks like from the outside - your repos, your actions, your dependencies, your exposure
- Attack condition alignment: Whether the conditions for a successful attack are present simultaneously across multiple domains
- Temporal velocity: How quickly your risk posture is changing
- Ecosystem position: Whether your organization sits at a chokepoint (like Docker) or is a leaf node
A high vulnerability count with no attacker interest is different from a moderate vulnerability count with active attacker reconnaissance. The OAIS captures this distinction - it’s a predictive model of adversary behavior, not a vulnerability counter.
Cross-Domain Correlation - Real Scenarios
The power of multi-domain monitoring becomes concrete through examples:
Scenario 1: Dark web credential + CI/CD vulnerability. ThreatCert’s Dark Web Intelligence detects that a maintainer of a popular GitHub Action has had credentials appear in a data breach dump. Simultaneously, CI/CD Pipeline Intelligence shows that 500 repos in your vendor chain depend on that action with mutable tags. Either signal alone is informational. Together, they indicate that the conditions for a supply chain compromise through that action are actively aligning. ThreatCert escalates the combined signal before the compromise occurs.
Scenario 2: DNS takeover + CI/CD curl-pipe-bash. A workflow downloads and executes a script from install.example.com. DNS Intelligence detects that the example.com domain has a dangling CNAME record pointing to a decommissioned cloud instance. An attacker can claim that cloud instance, serve a malicious script, and every CI run that curls from that URL executes the attacker’s code. Neither the CI/CD finding (RGS-006) nor the DNS finding alone tells the full story - the correlation does.
Scenario 3: Social media impersonation + maintainer account. Social Media Intelligence detects a new GitHub account impersonating a well-known action maintainer - same avatar, similar username, actively opening issues on popular repos. CI/CD Pipeline Intelligence shows that the real maintainer’s action is used by 1,000+ repos unpinned. The impersonation campaign may be the social engineering precursor to a credential compromise. ThreatCert correlates the impersonation signal with the supply chain exposure and alerts before the compromise attempt.
These scenarios aren’t theoretical. They’re the kind of multi-domain attack preparation that single-domain tools - including standalone CI/CD scanners - systematically miss.
2-3 Hop Vendor Chain Monitoring
Runner Guard scans your repos. ThreatCert goes further - it monitors your entire vendor supply chain across all intelligence domains, not just CI/CD.
The supply chain crisis demonstrated that your security depends on the security of your dependencies. SHA pinning protects you from tag manipulation, but what about the vendor behind the action? What about their network security posture, their DNS hygiene, their TLS configurations, their exposure on dark web forums? A compromised vendor doesn’t just mean a bad commit - it means an organization whose security has degraded across multiple dimensions simultaneously.
ThreatCert monitors your vendor chain 2-3 hops deep, every 60 minutes, across all active intelligence domains:
- Hop 1: Your repos and their direct action dependencies
- Hop 2: Your actions’ own CI/CD pipelines and their dependencies
- Hop 3: Foundational infrastructure - the build tools, the package managers, the registries
At each hop, ThreatCert doesn’t just scan for CI/CD vulnerabilities. With vendor authorization, you see the full ThreatScore across every intelligence module - CI/CD pipeline security, network exposure, DNS health, TLS posture, and web application risks. A vendor with clean CI/CD pipelines but an expiring TLS certificate and dangling DNS records is telling you a story about organizational security priorities. A vendor whose network exposure score has been degrading over 90 days while their maintainer count drops from three to one is telling you a different story - one about an organization that may be losing the capacity to respond to a security event.
This is the difference between monitoring your supply chain for known CI/CD vulnerabilities and understanding the actual security posture of the organizations you depend on. When a dependency’s overall threat score starts climbing - not just a new CVE, but a pattern of degradation across network, DNS, and CI/CD simultaneously - ThreatCert alerts you before the compromise reaches your pipelines.
The 50K Scan Proves the Model
This research campaign is the strongest argument for continuous monitoring:
- We scanned 50K repos and found 192,776 findings. That number is already wrong - repos have changed since the scan completed.
- We found 20,265 vulnerable repos. Some have been fixed since. Some have gotten worse. We don’t know which without re-scanning.
- The 2020 inflection shows that new repos have higher vulnerability rates than old ones. The problem is getting worse, not better - and only continuous measurement shows the trajectory.
- The AI force multiplier compresses attack timelines from days to hours. A weekly scan won’t catch an attack that executes and cleans up in four hours.
The data we’ve published through this series is a service to the community - a snapshot that reveals the scale of CI/CD security risk. But a snapshot, by definition, is frozen. Continuous monitoring is the live feed.
The Funnel
The series of articles traces a natural path:
- Read the research (this series) - understand the scale and nature of CI/CD security risk
- Scan your repos with Runner Guard - free, open-source, immediate results
- Realize point-in-time isn’t enough - pipelines change, dependencies shift, attack conditions align
- ThreatCert: 7 domains, 60-minute cycles, 2-3 hop vendor chain - continuous monitoring that treats CI/CD as one dimension of an integrated threat landscape
Vigilant open-sourced Runner Guard so anyone can scan their repos. We built ThreatCert for organizations that need that scan running every hour, correlated with six other intelligence domains, across their entire vendor chain.
Why CI/CD Is Different From Other Security Domains
Organizations have accepted continuous monitoring for network security (IDS/IPS), endpoint security (EDR), and cloud security (CSPM). CI/CD is the gap.
The argument for continuous CI/CD monitoring is stronger than for most other domains:
Higher rate of change. Network configurations change slowly - firewall rules, routing tables, DNS records update incrementally. CI/CD pipelines change rapidly - developers modify workflows with every feature, every release, every new tooling adoption. The higher the rate of change, the faster a snapshot goes stale.
Supply chain dependency. Your network security depends on your own configurations. Your CI/CD security depends on thousands of third-party action maintainers. When a single-maintainer action like action-gh-release receives a new commit, your security posture potentially changes - without you doing anything. Continuous monitoring catches these external changes. Point-in-time scanning can’t.
No perimeter. Network security has perimeter concepts - firewalls, NATs, DMZs. CI/CD has no perimeter. Workflow files are public. Actions are pulled from public repositories. Credentials flow through shared infrastructure. The attack surface is fully exposed, all the time, to anyone who can read a YAML file. Continuous visibility into this permanently exposed surface isn’t optional.
Attacker speed. As we documented in AI Agents as Force Multipliers, AI-paced CI/CD attacks can execute in hours. The monitoring frequency needs to match the attack speed. Annual audits worked when attacks were slow. They don’t work when attacks are autonomous.
What You Can Do Today
-
Scan your repos with Runner Guard. Start with the point-in-time assessment. Know where you stand right now.
-
Fix what Runner Guard finds. Use the Fix It guide to resolve findings - most take minutes.
-
Add Runner Guard to your CI. Run it on every workflow change so new vulnerabilities are caught at the PR stage, before they merge.
-
Evaluate your monitoring posture. Ask: how would we know if one of our action dependencies was compromised today? If the answer is “we wouldn’t until the next scan” - that’s the gap continuous monitoring closes.
-
Consider ThreatCert for continuous coverage. If your organization depends on open-source CI/CD infrastructure (and in 2026, every organization does), the question isn’t whether to monitor it - it’s how often.
The 50K scan revealed the problem. Runner Guard makes the scan accessible. ThreatCert makes it continuous. Together, they cover the full spectrum from awareness to ongoing protection.
Related Articles
From snapshot to continuous.
Runner Guard showed you the problem. ThreatCert solves it - continuous CI/CD pipeline monitoring, Temporal Shift Analysis, Attack Condition Alignment Detection, and Organizational Attacker Intent Scoring across your entire vendor chain. Every 60 minutes.
The detection capabilities described above are active across Vigilant client environments today. If your organization wants to assess its current exposure to this attack chain — or understand how our managed services align to your specific environment — contact your Vigilant account team or reach us at vigilantdefense.com.
This event reinforces what Vigilant has long asserted:
Nation-state adversaries are not probing our networks — they are preparing battlefields.
Stay alert, stay aggressive, stay Vigilant,
Chris Nyhuis
CEO, Vigilant

Vigilant, 7570 Bales Street
Suite 250, West Chester
Ohio 45069, United States
855-238-4445
Background
CEO of Vigilant, a global cybersecurity firm he has led for 16 years. 30+ years of experience across offensive security, SCADA/IoT, and critical infrastructure defense. Holds multiple patents including Forensically Validated Detection Systems and Secure Protocol Translation. Former instructor at a US intelligence school. Certified human trafficking investigator and OSINT practitioner. Vigilant dedicates 25% of profits to combating human trafficking, child exploitation, and supporting orphan care worldwide.
