From Scanner to Weapon: Inside the Supply Chain Attack That Backdoored the #1 AI Key Management Library
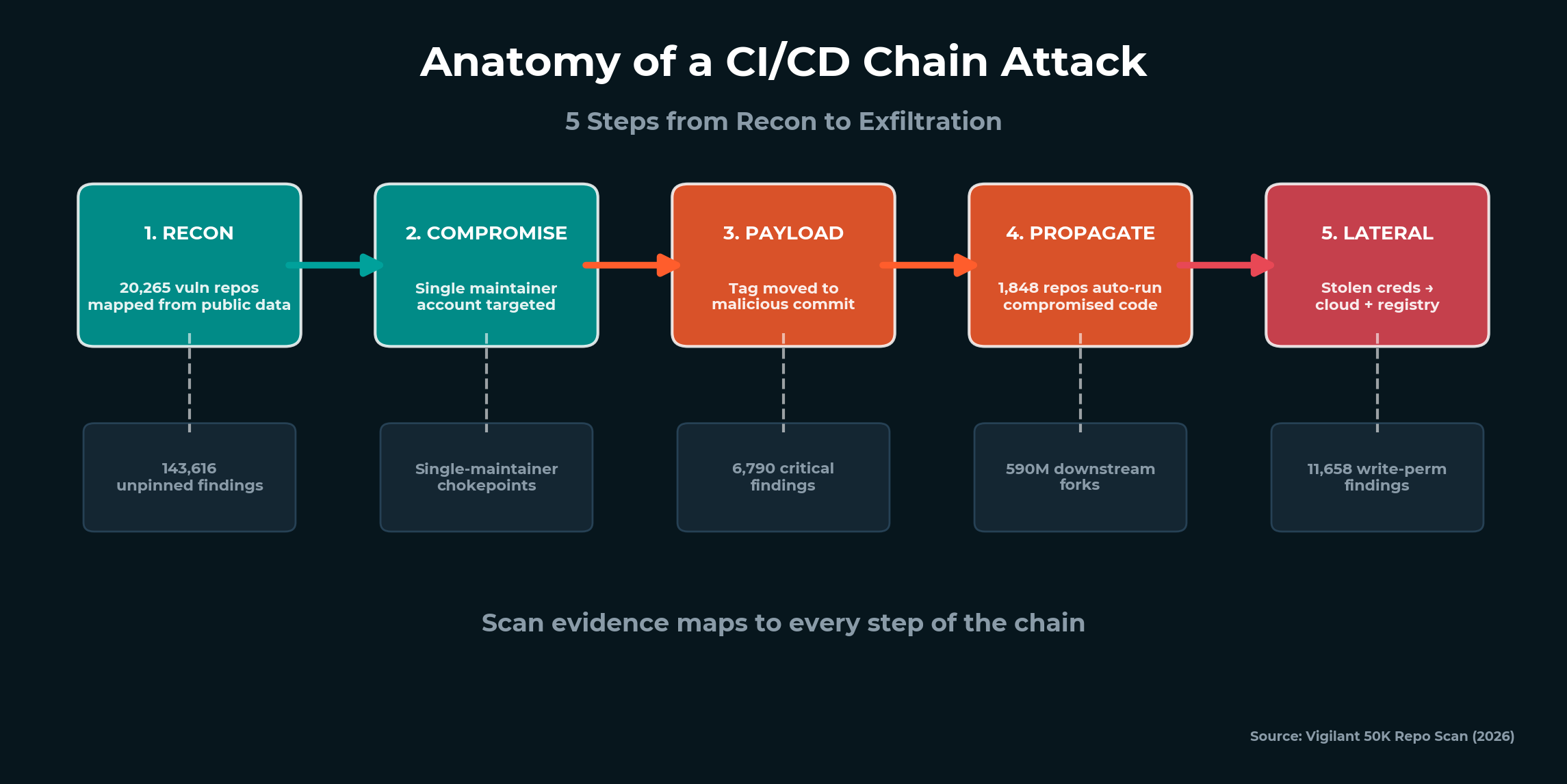
Vigilant breaks down the Trivy-to-LiteLLM supply chain attack chain step by step. How attackers compromised a vulnerability scanner, stole a PyPI publish token, and backdoored 97 million monthly downloads worth of AI infrastructure. Plus: the 50K-repo scan that found it first.
Read analysis →